 Image via WikipediaRooting enables an Android phone owner to do interesting things with his hardware. Let me write a few: performing whole-system backups, upgrading the operating system found on the device, removing clutter from the default install, even underclocking and overclocking become possible. These procedures are especially attractive when the phone manufacturer decides to no longer support the device with any software updates.
Image via WikipediaRooting enables an Android phone owner to do interesting things with his hardware. Let me write a few: performing whole-system backups, upgrading the operating system found on the device, removing clutter from the default install, even underclocking and overclocking become possible. These procedures are especially attractive when the phone manufacturer decides to no longer support the device with any software updates.Unfortunately, doing such a procedure usually voids any warranty you may have on your phone, so all responsibility rests on your shoulders.
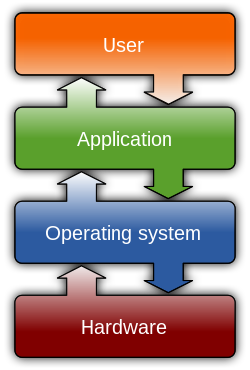
OK, why the name rooting? On UNIX-like operating systems like *BSDs and Linuxes such as Android, root denotes the do-all super-user on the machine. That means it can modify almost any file, anywhere. Getting this privilege level is therefore essential for manipulating protected files! A modern operating system has methods for entering such a privileged state but they are missing on Android. To make matters worse, the OS by design limits non-privileged code from attemting any other privilege escalation methods. All is not lost, however, since operating systems are usually so big, that there's bound to be some weak code, which can be exploited to cut the flow of normal execution and execute the exploit's code instead.
Here enters an exploit. It exploits some specific functionality of the OS' kernel which has been vulnerably implemented. Such code is found all the time by security researchers, hobby hackers and also malevolent crackers, but more importantly more or less quickly patched by software authors. Because security software updates are relatively unneeded on Android due to the isolationist application model, updates for phones are rare or even non-existent and usually focus on improved functionality.
That should be enough backround information, onto a specific procedure! My HTC Tattoo uses Linux version 2.6.29, which is rather old and vulnerable. An exploit exists for it! Good, now a would be hacker also needs a shell to run this program in. The application model on Android doesn't run software stored as native processor code but the software developer kit for Android does. Once you have it extracted, open a terminal, navigate to that folder and connect your phone to the PC in debugging mode. To see if the phone is accessible run:
./adb devicesThis should give you a serial number and a "running" status. Cool, now you can upload the compiled exploit file (find it on xda-developers) to your phone:
./adb shell "mkdir /data/local/bin" ./adb push path/on/PC/to/m7 /data/local/bin/m7 ./adb shell "chmod 755 /data/local/bin/m7"Now you can enter a full shell running on your phone and actually execute the exploit:
./adb shell cd /data/local/bin while ./m7 ; do : ; doneAfter a while you should be greeted by a # sign, the tell-tale mark of full privilege! But nothing works. That is because the way you got to the root shell is highly non-standard and the interpreter knows not where to look for commands you type in. To remedy this, type:
# export LD_LIBRARY_PATH=/system/lib # export PATH=/system/bin # idThe last command should confirm you are root with user id zero. Congrats! But know that what you have just accomplished is just a temporary root. It will only work for this shell session.
To have a permanent privilege escalation mechanism similar to more feature-full GNU/Linux distributions and that works whenever, you must install a program within your root shell called su, short for super user. You can find one here, but please install the Superuser app as well. Upload the su program the same way you uploaded the exploit file, with adb push. Once in the root shell, you must remount the system partition in the phone as writeable, because it is mounted as read-only by default:
# mount -o rw,remount /dev/block/mtdblock3 /system # cat /data/local/bin/su > /system/bin/su # chmod 6755 /system/bin/suNow reboot your phone.
# rebootOnce the phone completes the start up process it should be exactly the same as before, but with one added mechanism: the su program. The problem now is that any program can launch su and become the superuser so your first step to control its use should be to install an app called Superuser (it's also on the Android Market). For usage instructions see link. It's pretty simple though - if any non-approved app wants to run su, Superuser will be invoked to ask you if you allow or deny the requesting app such privileges.
Congratulations, you are now a mobile super user! :)



